Tips and key criteria for choosing a business VPN

Discover our all-in-one solution
A simple, poorly secured connection in an airport or a coworking space can be enough to compromise your entire internal network. Faced with this reality, choosing a corporate VPN is no longer just about securing a connection. Today, it is a question of intelligently orchestrating all the accesses to your IT ecosystem.
In this comprehensive guide, discover the essential criteria, mistakes to avoid, and the sure-fire way to select a VPN solution that's truly right for your business. The objective: to move from sustained security to operational fluidity where automation and centralization become your best allies.
What is a VPN?
A VPN (Virtual Private Network) is a technology that creates An encrypted tunnel between an employee's device and the company's servers. This tunnel protects data in transit against interceptions.
However, let's be clear: a Poorly administered VPN Create a Illusion of safety more dangerous than the absence of a VPN. Without real-time control and centralized management, this tool loses all its effectiveness.
Why use a secure professional VPN in business?
Adopt a Secure business VPN is no longer a technical option, it is a business requirement.

The challenges of cybersecurity for SMEs and ETIs
Les SMEs and ETI Are priority targets for cyberattacks. The lack of secure remote access is often the main gateway.A well-managed and synchronized IT infrastructure With fleet management tools (MDM) may significantly reduce risks linked to poorly secured remote accesses.
Let's take a concrete case: an SME with 50 employees using a poorly configured VPN, without automatic revocation of access when an employee leaves, exposes its entire customer database for months. To learn more about this critical topic, discover the challenges of cybersecurity in business.
Common corporate VPN use cases:
- Securing hybrid work: Protection of connections from public Wi-Fi networks.
- Access to business applications: Secure connection to internal servers (ERP, CRM) remotely.
- Protection of sensitive data: End-to-end communication encryption to ensure confidentiality.
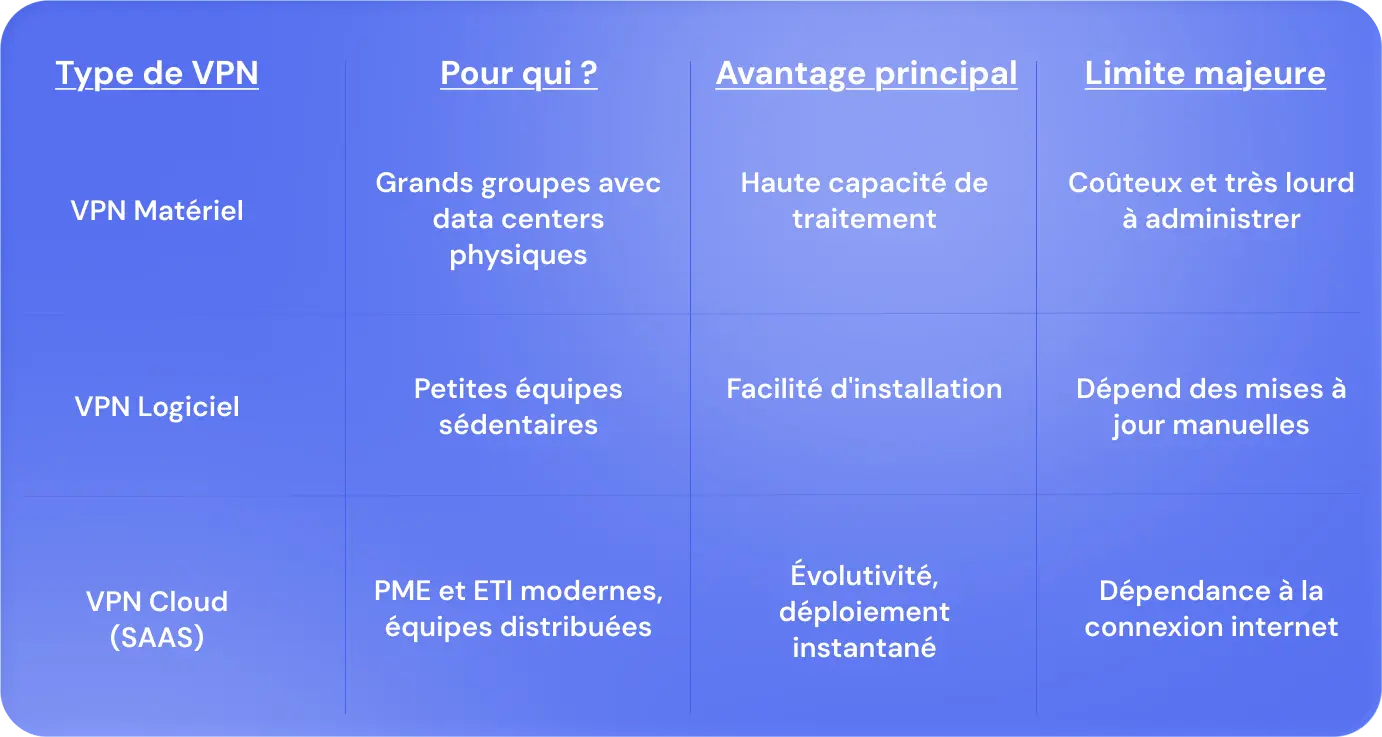
Comparing the different types of VPNs for business
The market is full of solutions, but not all are created equal. To find out how to choose a professional VPN, here is a clear comparison of existing architectures.
Hardware VPN
It is a dedicated physical box (firewall with VPN function) placed on your network. It is a robust solution, offering high performance for fixed sites, but complex to deploy for a mobile workforce.
VPN software
Installed directly on employee terminals, it allows great flexibility. This is the standard for modern businesses where teams work in a nomadic or hybrid mode.
Cloud VPN
The most agile solution. It offloads the management of VPN servers to managed services in the cloud. This allows immediate scalability, ideal for growing businesses.
European sovereign solutions vs international solutions
For a company concerned about the protection of its data, the choice between an international solution (sometimes subject to the Cloud Act) and a European solution is strategic. European solutions guarantee legal sovereignty and facilitated GDPR compliance, a strong argument for European SMEs and ETIs.
Criteria for choosing the best VPN for your business
To find the best VPN for your business, your thinking must be based on technological and organizational criteria:
Security and encryption protocols
Demand cutting-edge standards. IPsec VPN and SSL VPN protocols are essential for military-grade encryption. Also, make sure that the solution integrates multi-factor authentication (MFA).
Centralized management and ease of IT administration
In a centralized SaaS environment, IT doesn't have to be a burden. Choose an all-in-one platform offering a single dashboard to monitor connections, identify anomalies and manage licenses.
Cross-platform compatibility and integration with your IS
Your VPN should be cross-MDM and cross-OS. It should integrate seamlessly with your HRIS connectors to automate the creation and removal of accesses based on HR movements.
Performance, bandwidth, and stability
A VPN should not hamper productivity. Latency should be minimal. Test the stability of the servers, especially if your employees access heavy applications or in real time.
Technical support, support and GDPR compliance
Beyond the technical side, make sure that the support is responsive and able to support your teams. GDPR compliance should be set in the stone of your supplier.
The cost
Consider the total cost of ownership (TCO): licenses, maintenance, human time required for administration. The cheapest VPN is often not the most profitable in the medium term.
How do I deploy a corporate VPN? Key steps
Needs analysis and IT audit
Before any deployment, carry out a IT asset audit to identify current vulnerability points and the real needs of your users.
Selecting the right solution
Compare solutions according to the criteria mentioned above, with an emphasis on integration with your existing fleet (e.g. MDM compatibility).
Deployment, onboarding, and maintenance
Don't deploy all at once. Proceed in waves, train your employees in best practices and automate access management via your monitoring tool.
How does Rzilient help businesses with cybersecurity and the choice of a VPN?
Choosing the right network architecture is complex. rzilient helps you choose your VPN to transform this security constraint into a performance driver. We analyze your flows, secure your remote accesses and integrate your security tools into unified management.

FAQs about choosing a business VPN
What are the differences between a corporate VPN and a personal VPN?
A personal VPN protects an individual's privacy by masking their IP. A corporate VPN secures access to a complex internal network, manages hundreds of identities, and provides centralized management for IT teams.
Can a VPN be combined with other security tools?
Yes, it is even imperative. The 2026 Business VPN integrates with next-generation firewalls, Endpoint Detection and Response (EDR) solutions, and Mobile Device Management (MDM) platforms for comprehensive security.
How do you ensure GDPR compliance with a VPN?
Opt for a sovereign provider whose servers are located in Europe, which applies a strict no-log policy and which integrates the principles of Security by Design.
Is a VPN enough to protect the entire IT infrastructure?
No It is a fundamental building block, but security requires a holistic approach: access management, secure fleet, intelligent IT agent for monitoring, and employee awareness.
.webp)
